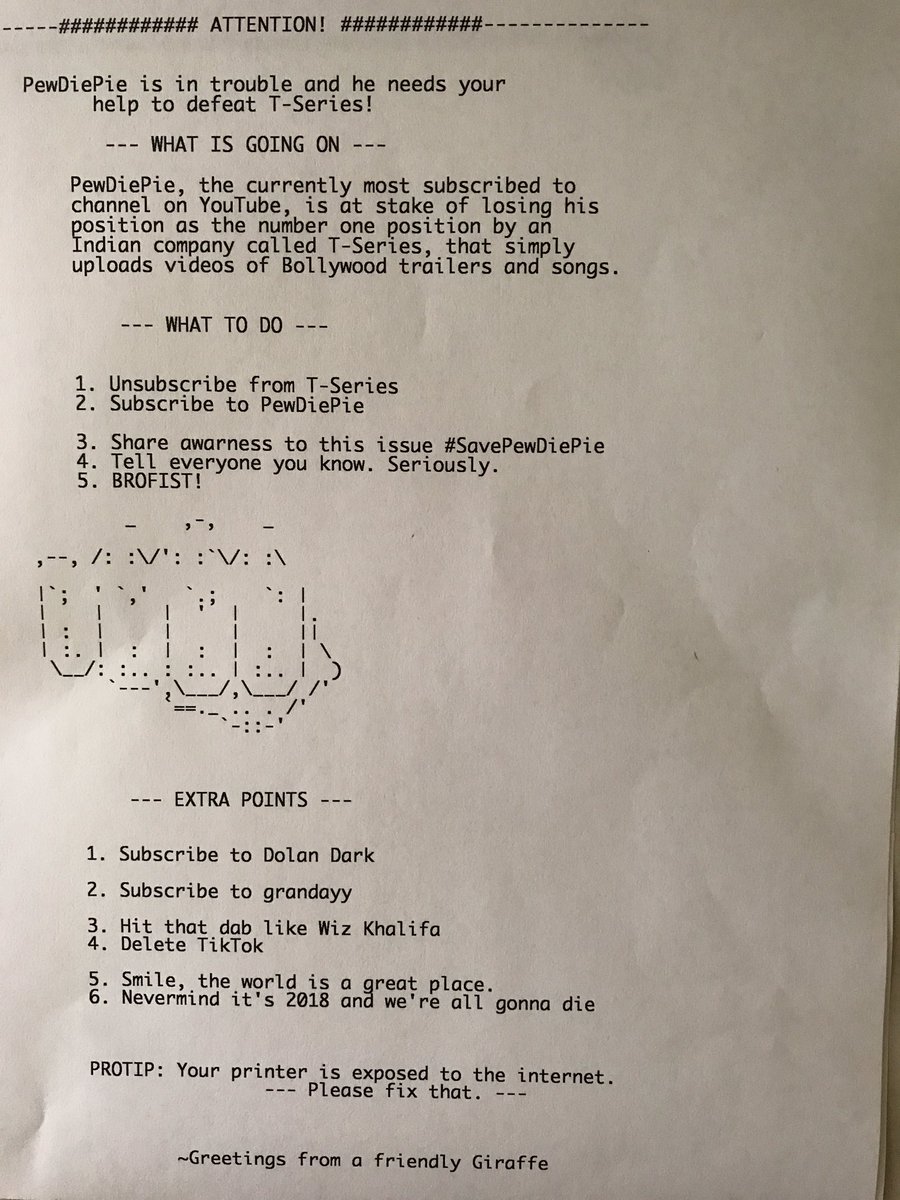
TheHackerGiraffe & PewDiePie Printer Predicament Using The Printer Exploitation Toolkit PRET - YouTube

Insights from the PewDiePie Hack: Trends in Strengthening Public Sector Printer Security – Connected IT Blog

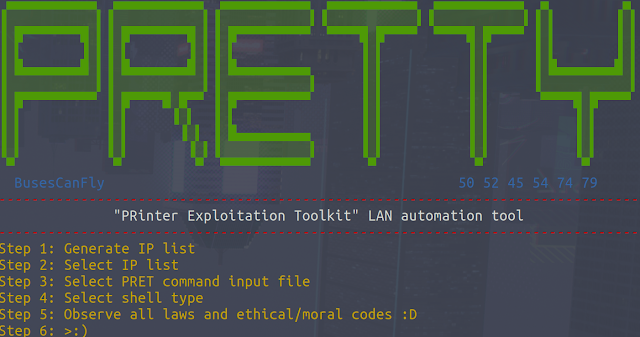
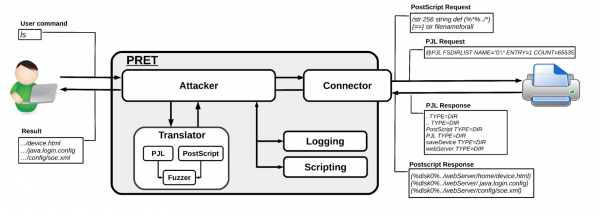
National Cyber Security Services - PRETty:-- "#Printer #Exploitation # Toolkit" #LAN #automation #tool. #PRETty is useful when a large number of printers are present on a #network. Instead of #scanning, logging, and manually